Cyber Liability Readiness
Cyber Liability Readiness Standard
Manage compliance with your cyber liability insurance policy while you manage all your other IT Security Requirements. Don’t suffer a denied insurance payout as the result of a failed post-breach audit.
Download DatasheetUnderstand the Risks Associated with Cyber Liability Insurance
With an alarming uptick in data breaches and ransomware in recent years, an increasing number of organizations have opted to acquire cyber risk insurance to protect themselves against catastrophic loss. However, as the threat landscape continues to expand, many insurance companies are including more IT security requirements in their applications. While some of these are clearly stated, others are hidden within confusing policy documentation. In the event of a breach, the insurance company WILL perform an audit of your IT security policies, procedures and evidence of compliance, looking for any reason to deny the claim.
Understand the Requirements, and Ensure Compliance using Compliance Manager GRC
Compliance Manager GRC now includes a cyber risk insurance readiness standard designed to help organizations meet the IT requirements of most common cyber risk insurance policies. The standard consists of a superset of the most common cybersecurity requirements included in a majority of Cyber Risk Insurance policies. And, as with all Compliance Manager GRC standards, you can easily customize the cyber risk insurance standard to exactly match the requirements of your specific policies.
Get a DemoReduce the Likelihood of a Data Breach, And Increase the Likelihood That Any Claims Will Be Approved
If the person paying the bills is shelling out money in the form of insurance premiums to cover losses in the event of a cyberattack or data breach, the last thing they want is a battle with the insurance company to collect their payout. As the IT person in charge of the technical infrastructure, you’re in the hot seat. Compliance Manager GRC reduces the likelihood there will ever be a need to file a claim in the first place since the software proactively discovers issues and risks and creates a management plan to quickly address them. If a breach does occur, you can quickly and painlessly supply the evidence of compliance that the insurance company will demand.
Automatically Generate Evidence of Compliance as Part of Your Daily Activities
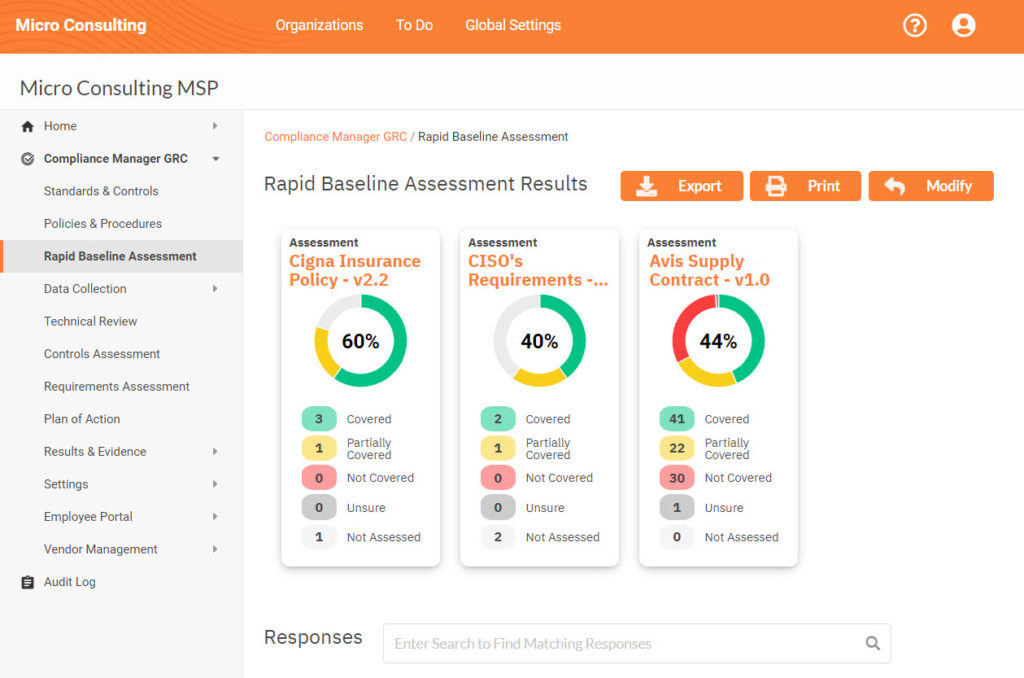
Compliance Manager GRC helps you document all the things you are doing to protect the network(s) you manage. Run a Rapid Baseline Assessment against the cyber insurance readiness standard to see what’s required, and how well you are meeting those requirements. The system will automatically generate for you a comprehensive Policies & Procedures manual for you to follow.
Next, perform a more comprehensive assessment by running the automatic data collectors which will serve as your evidence of compliance for some of the policy terms. And for everything else, you can upload any supporting documentation right into the system so everything you’ll need in the event of an audit can be retrieved instantly, and with zero panic or hassles.
EFFECTIVELY MANAGE CYBER RISK INSURANCE COMPLIANCE
Most MSPs and IT Departments don’t get involved in cyber insurance policy compliance because they usually aren’t asked. And even if you are, it’s hard to keep that activity top-of-mind when you’re handling your day-to-day job. Compliance Manager GRC makes it easy to track and comply with insurance policy terms because you do it hand-in-hand
MANAGE END USER/EMPLOYEE RISK
Many data breaches are the result of end users making simple mistakes that create vulnerabilities on your network. And many insurance policies require at least basic Security Awareness Training. Compliance Manager GRC includes an Employee/End User Portal to track and enforce employee security awareness training and corporate security policy attestation.
MANAGE BUSINESS ASSOCIATE RISK
Whether you’re an MSP, or an IT Department that provides administrative access to outside consultants or vendors, your risk just expanded. Compliance Manager GRC includes a unique vendor risk management portal. It allows you to make sure that any vendors who have access to your sensitive information are also in compliance with whatever terms your policy requires.
Overcome the Biggest IT Challenges and Responsibilities
- Reduce Risk
- Reduce Complexity
- Save Money