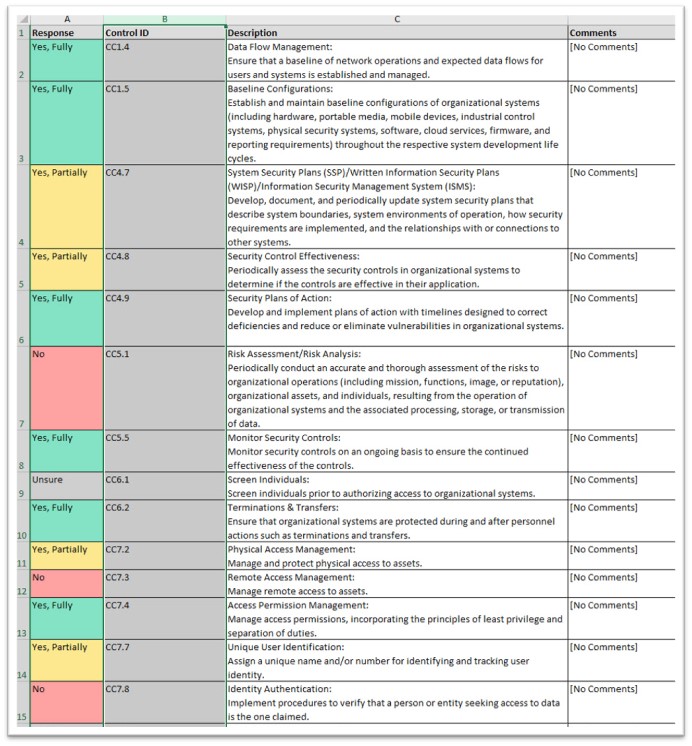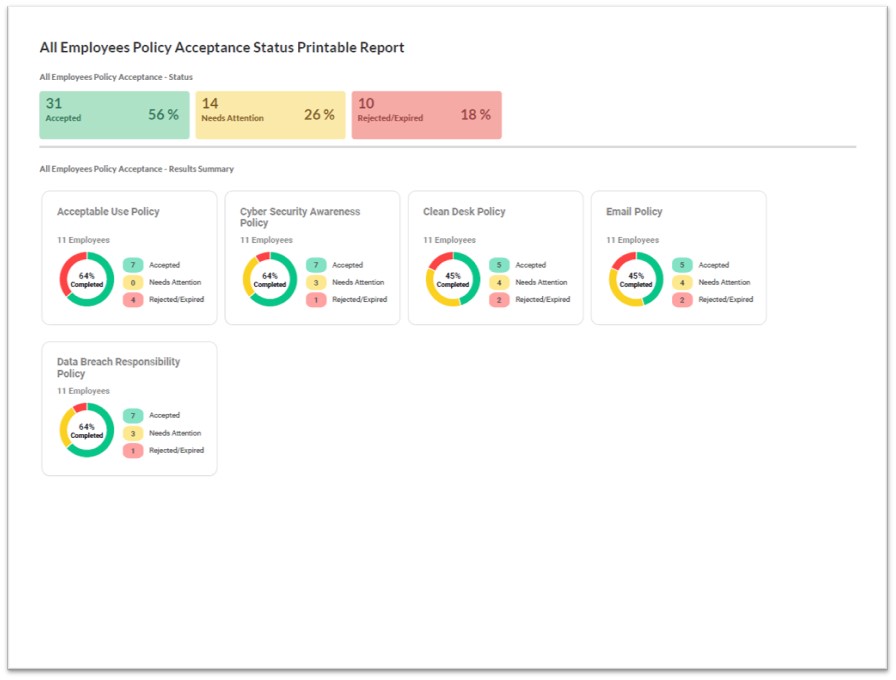
All Employees Policy Acceptance Status Report
Compliance Manager GRC includes the ability to upload any number of policies or other HR-related documents into a self-serve web-based portal that employees can log-into, read and review the documents, and attest to agreement with the contents. This dashboard report presents a summary of Employee Policy Acceptance results recorded for all employees of a given organization. Information is continually tracked and updated in real time in the Compliance Manager GRC Site’s Employee Tracker Dashboard.